One challenge that many organizations face when using self-hosted Prometheus is that all users have the same level of permissions. As a result, one user may inadvertently break another user’s dashboards or alerts, wreaking havoc on the monitoring environment. As many of our customers come to Chronosphere after running Prometheus internally, we’ve been working on ways to tackle this challenge in our offering.
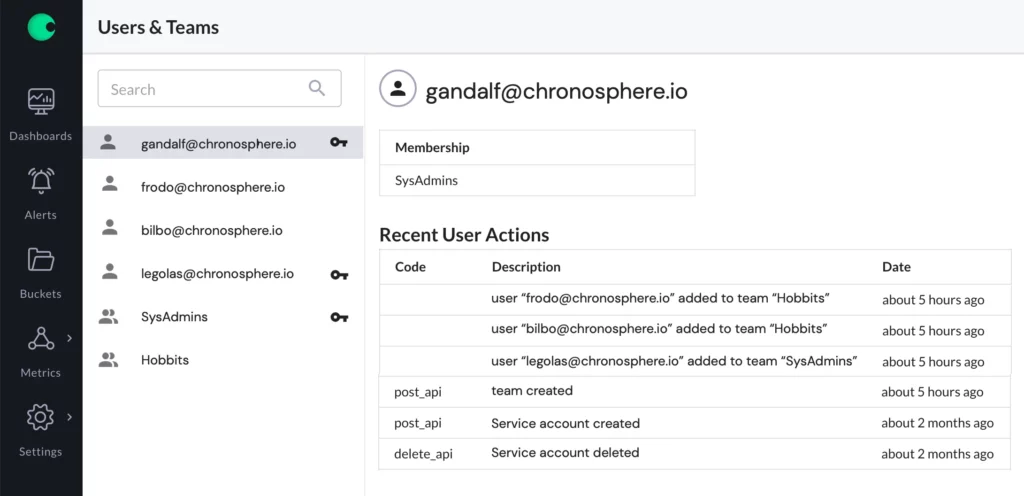
Today we are happy to announce new capabilities in Chronosphere that make it easier for central observability teams to safely scale Chronosphere deployments across their organizations, which is the first step to solving these challenges. The new capabilities allow administrators to group users into Teams, and to assign certain teams the role of SysAdmin within Chronosphere.
These two enhancements provide the foundation for a stable and secure monitoring environment anchored by Chronosphere’s SasS application. A quick summary of the capabilities:
- Teams enables you to mirror your organizational structure within Chronosphere, and longer-term increase productivity.
- SysAdmin restricts sensitive operations such as the creation and management of users and teams to trusted super-users.
Teams
If you work at an organization, most often than not, you are part of a team. Teams enable companies to be more flexible and productive, push down responsibilities and decision making to team members and build trust and enhance relationships between team members. Because our customers often think about their environments in terms of teams, we have added the organizational construct of teams to reflect your reality. Our goal is to enable you to be more productive when using Chronosphere. With this new release, you can display team information in Chronosphere and synchronize it on a consistent basis using our command line interface.
SysAdmin
In this update we also introduce our first role, the SysAdmin role. This is akin to the root user in a Linux System and it is a role that is suited for the Central Observability team members or the person you elect to be the Chronosphere administrator. Because roles and individuals within an organization are dynamic, instead of associating SysAdmin privileges to an individual, it is assigned to a team. This gives members of that team the ability to perform system-wide sensitive operations that should only be entrusted to knowledgeable users. In this release the operations that are restricted to SysAdmin users are inviting users to your Chronosphere deployment and creation of teams and manipulation of team membership. Gating these operations behind trusted users allows you to work on Chronosphere without wondering if users are present or if someone was accidentally deleted, which can happen when these kinds of operations are available to every user of the system. This team is an advantage compared to offerings such as open source Prometheus where there is no team model and, therefore, sensitive operations are open to all users.
Team creation and team membership manipulation is just the first set of sensitive operations that will be gated behind the SysAdmin role. In the future, you will see more operations added to further provide peace of mind for other parts of the Chronosphere application. Some examples of these operations are the ability to set policies around metrics data aggregation, retention, and relabeling.
Conclusion
SysAdmin and Teams are just the first steps in a series of capabilities that we’re planning that are all aimed at helping you securely scale your Chronosphere deployment while also increasing productivity. Watch this space for further news about our future releases.